Updates and patches: what are we talking about?
Updates are often perceived as a constraint and neglected by users. They often fall at the wrong time: during a work session, during an outing with friends... However, they are essential to ensure your computer security. They allow you to correct security flaws. Without a patch, you keep the door open for a cyber attacker.
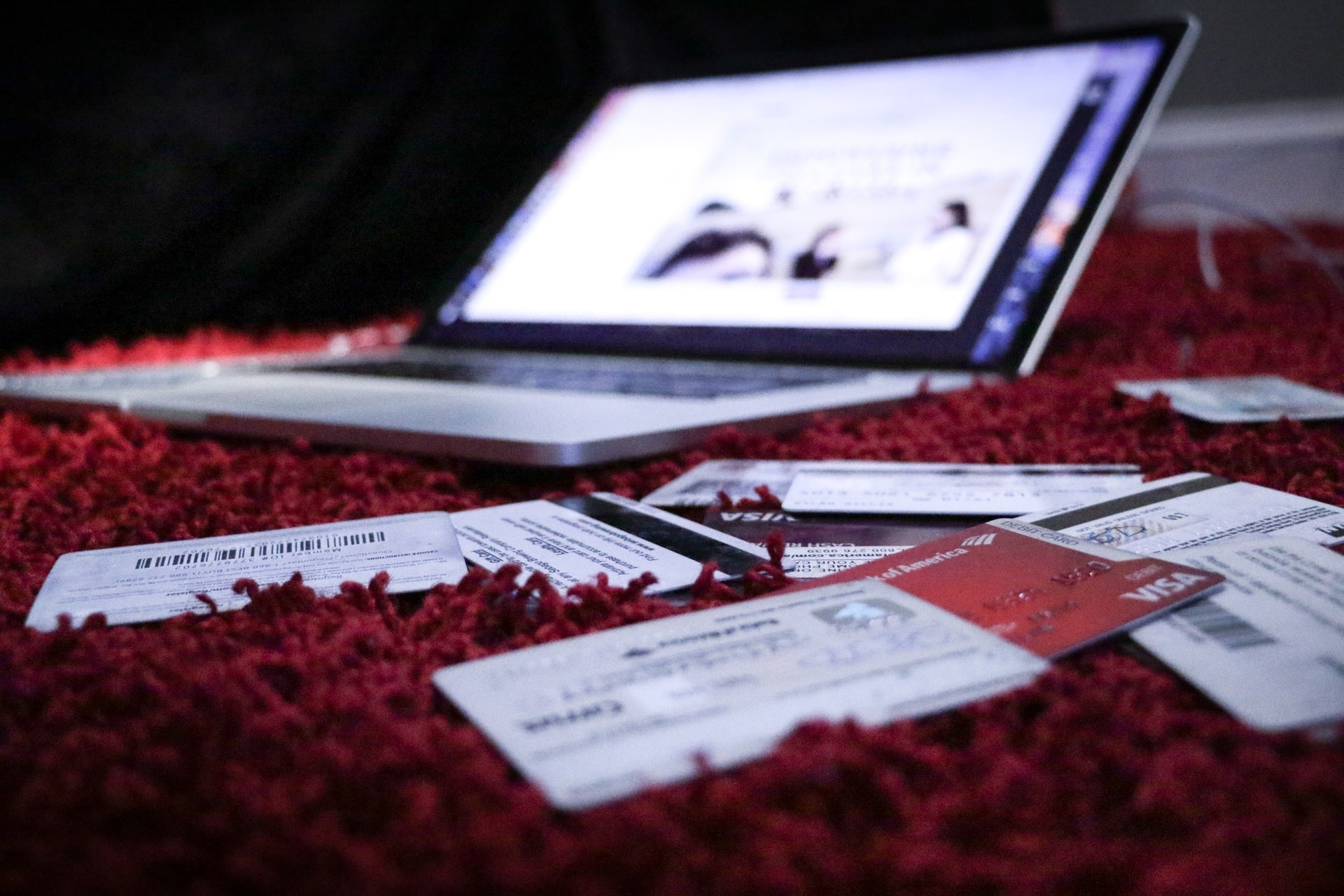
A security flaw is a breach through which a cyber attacker has the possibility to access your device or software and take control of it. The main risks are theft of personal data, online account hacking and identity theft, or even embezzlement of your money.
A study conducted by Harris Interactive and CaptainCyber on a sample of 648 company employees reveals that 88% of them would promptly apply their updates. A practice of cyber hygiene that seems to be widespread. The question is what is meant by "promptly".
There are two types of updates: the security update and the feature update.
The first is the release of a corrected version of a software or operating system of a device that protects against security flaws identified in the previous version. It allows to correct security flaws, i.e. bugs that can be exploited by attackers.
The second is the release of a more advanced version of a software or operating system of a device. It also allows to install new features, to correct non-exploitable bugs, to simplify the user experience, etc.
Why is it dangerous to neglect updates?
As mentioned in the Cyberbrief of February 23, analysts from NCC Group, a British cybersecurity company, published a report on vulnerabilities in self-service electric scooters. Attackers could exploit these flaws to produce several negative effects: increasing the maximum speed limit, but also retrieving information about the routes of previous users.
The flaws came, among others, from unpatched or unupdated applications, thus revealing vulnerabilities.
The medical sector has not been spared either. Last October, Medtronic, a medical technology company, issued an emergency recall of insulin pump remote controls. Poor cybersecurity of its devices was putting more than 30,000 diabetics at risk.
Another case: David Colombo, the founder of Colombo Technology, a cybersecurity company had stated on his Twitter account that he could execute remote controls on compromised Tesla vehicles without their owners' knowledge. Among the actions that could be performed: disabling Sentry Mode, opening car doors and windows, flashing lights and even starting keyless driving.
Last May, the UK's National Cyber Security Center also warned about the threat from corporate connected devices in a report. Laptops, smartphones, corporate printers, video conferencing systems, VoIP phones, and all connected devices used in a corporate environment are an attractive target for cyber attackers. These ECDs (Enterprise Connected Devices) allow them to steal sensitive and valuable data, gain significant monetary gain through ransomware attacks, and build a base for attack and positioning
While updates are beyond your control and are often the sole responsibility of the companies that market these devices, you should still check that they are in place for the devices and software you use.
So how to protect yourself from software flaws?
First of all, let's distinguish two very different situations: private and corporate.
In the private setting, you are the only one responsible for updating your devices and software.
On the other hand, in a company, the IT department is responsible for updating professional tools. For smaller companies, employees do it under the supervision of the company manager.
Here are the tips to follow to protect yourself from the software vulnerabilities mentioned:
- Update all devices and software as soon as possible. It only takes one un-updated device for cyber attackers to gain access to your entire digital environment.
- Download updates only from official websites. It is recommended that you check what you are agreeing to when installing an update, to avoid unwanted software. Do not download "pirate" or "warez" versions as these often contain malware.
- Identify all devices and software used. Some Internet Service Providers (ISPs) offer an inventory application to list the devices connected to your home or office computer network.
- Enable the option to automatically download and install updates as soon as the software allows.
- Schedule updates during periods of professional and/or personal inactivity.
- Beware of fake updates on the Internet Pop-ups can appear and encourage you to download updates that hide malware.
Be vigilant, even at work:
- Define the rules for performing updates. Make an inventory of the devices and software used, define how/where/by whom updates are performed.
- Find out about the regular release of updates from the editor. Check if the publisher or manufacturer regularly publishes updates and when they are released.
- Test updates when possible and make backups. Sometimes the updated solution becomes incompatible with the software or device. It's best to guard against this.
- Otherwise protect devices that cannot be updated. Devices that are too old, no longer under warranty, should still be taken into account by disconnecting them from the Internet, for example, to separate them from the rest of the computer network.
- Keep yourself informed of the existence of 0-days, these security flaws exploited by attackers, which were not known by the editor, and for which patches or workarounds may nevertheless be available. Every hour counts.
Take back control and become cyber vigilant
Do you want to protect yourself as best as possible from hackers? With CaptainCyber trainings (app available on the App Store and Google Play), get up to speed on the most common attacks and how to protect yourself from them 🛡.
Elisabeth, Human Resources Director tested the CaptainCyber trainings and confides:
"The CaptainCyber app is a good tool to democratize information security among our employees"
And you, what do you do to regain control?