Why do we need to make backups?
Every day, we create and accumulate a lot of digital data on different devices: computer, phone, tablet... If it is only kept on these media, the data is exposed to risks.
With little or no backup, you take the risk that your data is lost, stolen, hacked, damaged or destroyed. For example, imagine that your most precious family photos are stored on a hard drive and the drive fails. You didn't back them up to another medium, so the photos are gone. There is no way to go back. Another more serious case: your house catches fire and all the proof of purchase of your goods (computers, tablets) and other invoices that were inside have been reduced to ashes and everything has to be redone.
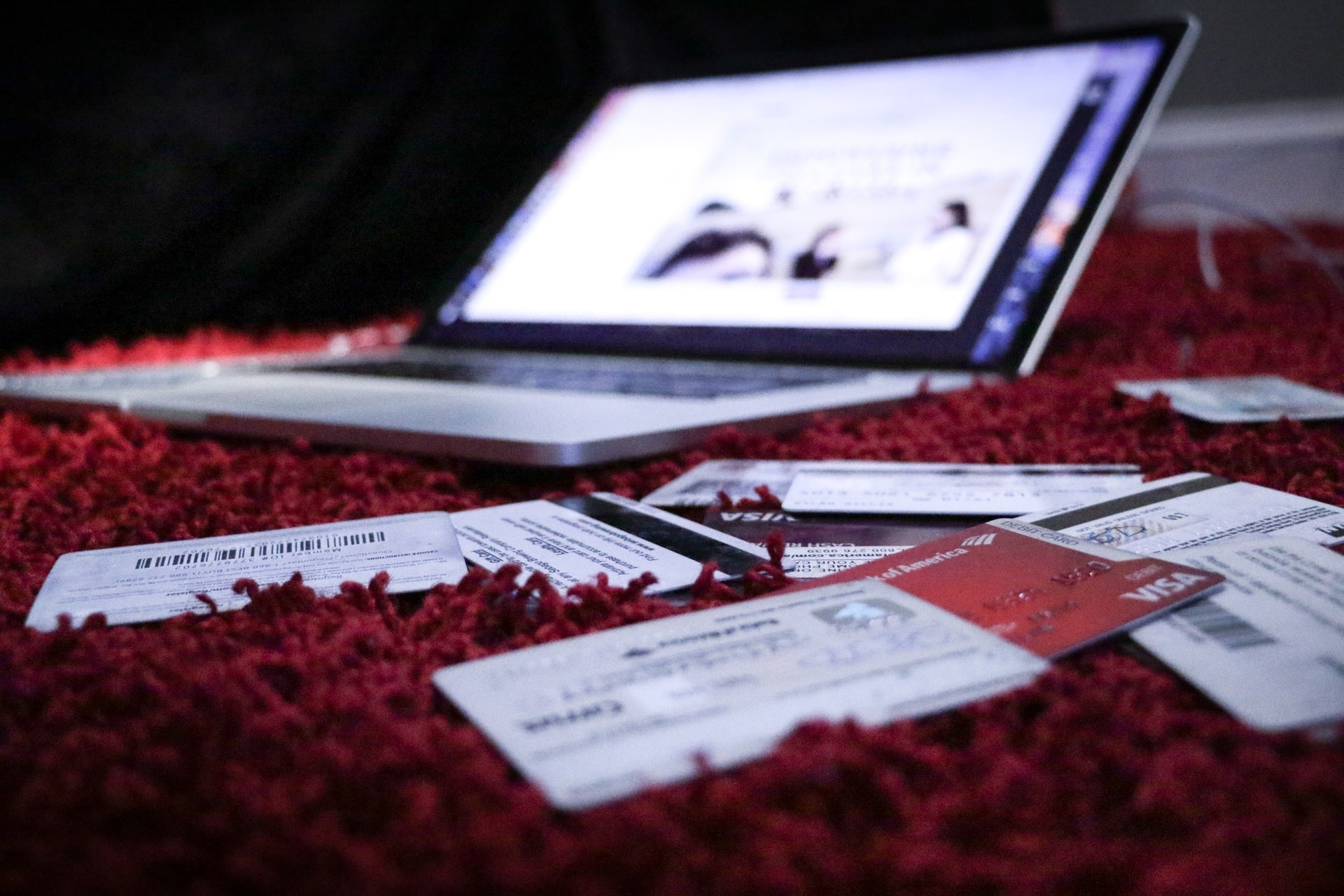
The backup allows you to protect yourself from data loss in case of mishandling, loss of equipment or other disasters. It is also the only way to recover data following a virus or fungus. Sufficiently recent backups, neither encrypted nor corrupted, are the key to recovering data and resuming activities without having to pay a ransom.
However, it is also important to keep your backups safe from cyber attacks. To do this, backup software increasingly offers so-called unalterable backups, generally referred to as "WORM" (write once, read many), to be used as a last resort. It is also possible to have disconnected backups.
As you can see, there are many reasons why your computer data can suddenly disappear, with no hope of finding it again... unless the backups have been made correctly. Moreover, computer equipment has a limited lifespan, whereas data is meant to be kept for the long term. Backup is therefore the best solution to preserve data, but it is important to learn how to do it efficiently.
Which data should be prioritized?
Not all data has the same degree of importance, whether on a professional or personal level. It is therefore necessary to select the data to be prioritized, because they do not all require the same frequency of backup.
A few simple but essential reflexes. Identifying the devices on which your data is stored is important in order to identify which data should be backed up first (files, images, videos, etc.). Several questions need to be asked: What data would not be recoverable in case of a problem with the device? What are the most frequently accessed and/or modified files? Now that you have a more hierarchical view of your data, it becomes easier to assess how often you should back up your data: a work file that you work on every day should be backed up several times a day, unlike a photo album that you view once a year. Unless, of course, your professional activity is to be a photographer.
What is the best backup solution?
There are many backup solutions and they can be grouped into two categories: external storage solutions (external hard drive, USB key, memory card, DVD) and online storage solutions (the "cloud" solutions, free or paid).
There are 4 criteria to consider when choosing the right solution:
- The frequency of backup: if a data must be frequently backed up, it is better to use an easy and automated backup solution. It is better to use the cloud in these cases and external storage solutions for more occasional backups.
- The size of the files to be kept: for heavy files such as photos or videos, using an external storage solution remains the best option, as it generally offers larger storage spaces and at lower prices.
- The price of the solutions: external storage solutions are to be paid directly at the time of purchase and are cost-effective in the medium/long term compared to online solutions. The latter are most often free, but become payable if you want more storage space, a customer support service, advanced features such as automatic backup, etc. They are offered in the form of a monthly or annual subscription most of the time.
- The risks to which they are exposed: The less you use a device, the less danger it is exposed to. External solutions are therefore more secure than online solutions, which are prone to cyber attacks (see below).
5 best practices to secure your data
- Disconnect storage systems from the network: a flaw in a connected device or storage system is enough for a cybercriminal to access your backups and your most precious data. He is then able to steal, destroy or encrypt them: we are talking about ransomware attacks or ransomware. In order to avoid these attacks on your backups, be sure to disconnect your backup solutions once your data has been copied.
- Protect your backups: take care of them, protect them from any risk of damage and copy your data on several media, in different places.
- Protect your backups: encrypt your backups and protect them with strong passwords.
- Test backups and replace obsolete backup media: copy backed up data to another device to ensure everything is in order. Anticipate how worn out your external or online media is and migrate your data before you lose it.
- Backup software that is essential to the operation of your data: Windows, iOS, Android... be sure to make backups of the operating system that allows you to read and operate your data.
You want to know more and become a cyber-hero?
Find soon the training "how to protect your data with backups" on our CaptainCyber application (available on the App Store and Google Play). In the meantime, learn how to master your passwords, strengthen your social profiles or protect your personal data!