For the cyber attacker, the only thing that matters is his own goal: to complete the attack. For a cybercriminal: to obtain the payment of the ransom, even if it means negotiating. Because the cost structure of the attacker is just like the business model of SaaS startups: the cost of attacking an additional company is close to zero. Worse: the attacker's operational risk is very limited, protected by several jurisdictions and many layers of technology between his target and his digital "benchmark."
Paradoxically, an attack could even be more interesting in a highly regulated context: because the ransomware operator will threaten to reveal the data leak to third parties (customers, authorities, media). Such "triple ransomware" will probably become a common modus operandi for the most "palatable" targets. In February 2021, the ransomware group REvil announced that it would add two steps to its extortion scheme: distributed denial of service (DDoS) attacks and phone calls to the victim's business partners and the media.
Don't let that stop us from making significant efforts toward compliance, because companies owe it to regulators and their customers. But it is dangerous to substitute cyber compliance for operational cyber security. Because operational cyber security is driven by three main metrics: average time to detection, triage and recovery. With the appropriate financial efforts.
Despite the cases of attacks and incidents observed over the last 20 years, with operating modes that are sometimes so similar in this period - as shown by the comparison of the operating modes of the attacks carried out by Kevin Mitnick, a young cybercriminal on his own, in 1994, and the one suffered by the giant Twitter in the summer of 2020, by teenagers - we do not sufficiently address the real causes. They lie above all in the organization of the cyber subject in the structures and more generally in its human factor. Because the cyber subject is a human subject that hides behind a technical problem (BCG). Or, more precisely, it is both an eminently technical problem and an eminently human problem. Hence its complexity.
It must be said that in the cyber domain, financial means are too rarely allocated according to the stakes. But in a reactive approach following an incident. Or corrective following an audit. However, it is important to proactively implement a true risk-based budgeting approach, as McKinsey advocates. And to go further: to build, train and challenge capabilities to deal with these risks, in the same concept as that of the military forces. This is not to be confused with the principle of cybersecurity certification: this applies to sensitive information systems, not to cybersecurity devices.
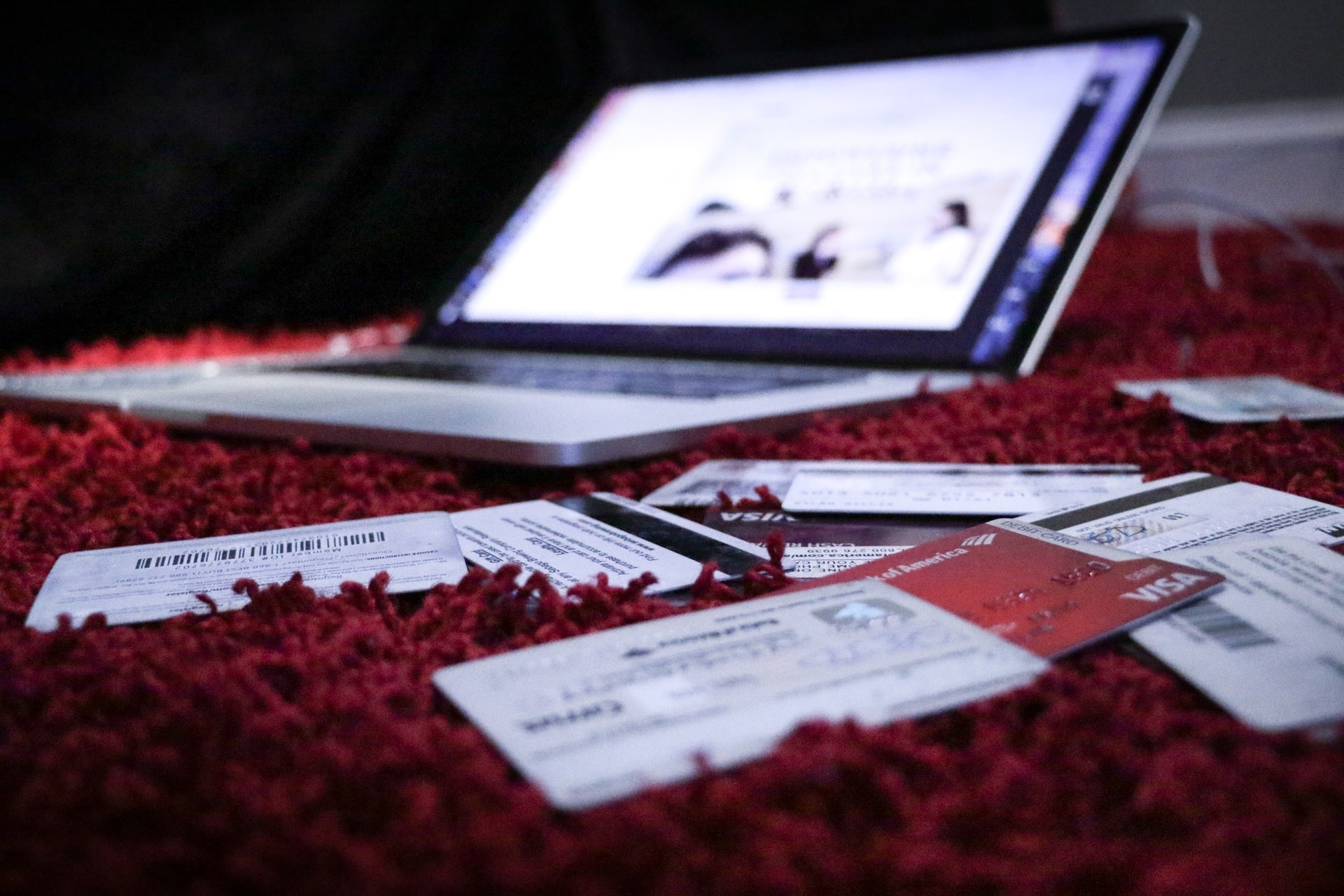
Among these risks, human origin represents 70 to 90% of the claims reported to specialized insurers, while only 1 to 2% of cyber budgets are really dedicated to the human factor. This is a shocking conclusion in itself:
Cyber expenses often boil down to: throwing money at a problem.
This will remain true until a robust method of assessing the effectiveness of cyber budgets (i.e., calculating ROI) is put in place in every company that wants to seriously address the subject. A method that not only looks at the risks (and losses, fraud), but also at the real savings and opportunities seized.